See What’s Happening Across Every Login & Session
Monitor user activity, detect anomalies, and identify risks early before they turn into incidents
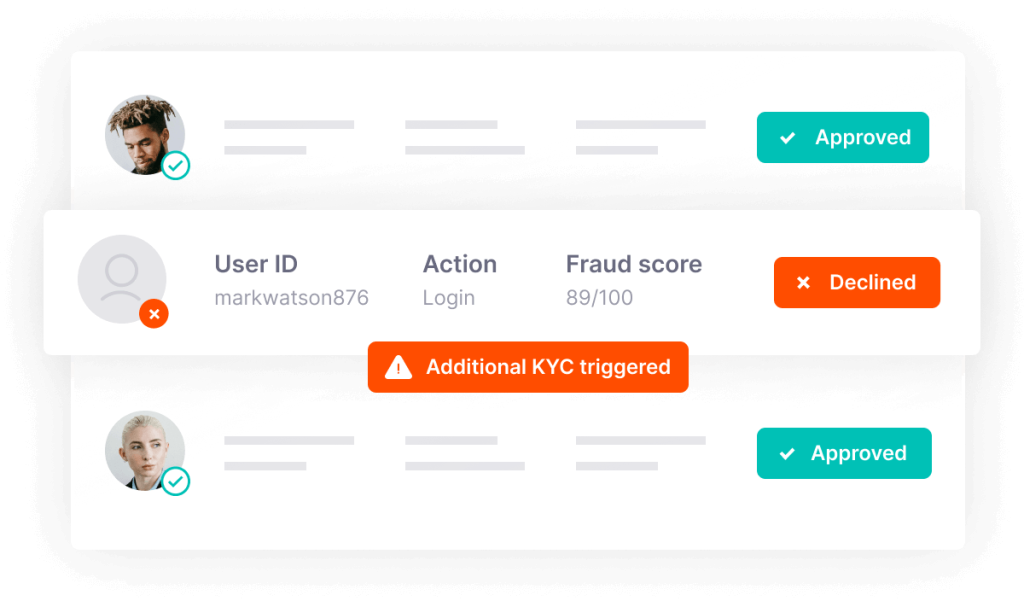
Prevent Fraud Losses
WHAT WE ACTUALLY DO
STEP 01
Activity Mapping
We review how login and user activity is currently tracked.
STEP 02
Signal Identification
We identify key behavioral and session signals.
STEP 03
Visibility Gaps
We pinpoint where activity is not being monitored.
STEP 04
Monitoring Strategy
You get clear steps to improve visibility and detection.
Securing Every Layer of Financial Risk
From account takeovers to AML compliance and identity verification, we provide the intelligence and controls needed to detect threats, prevent fraud, and protect assets across every stage.
Identity Verification
Most identity verification tools focus on validating documents, but lack the risk context needed